Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Deeploy
Deeploy brings order to AI chaos, helping you scale safely while staying compliant and in control of your systems.
Last updated: March 1, 2026
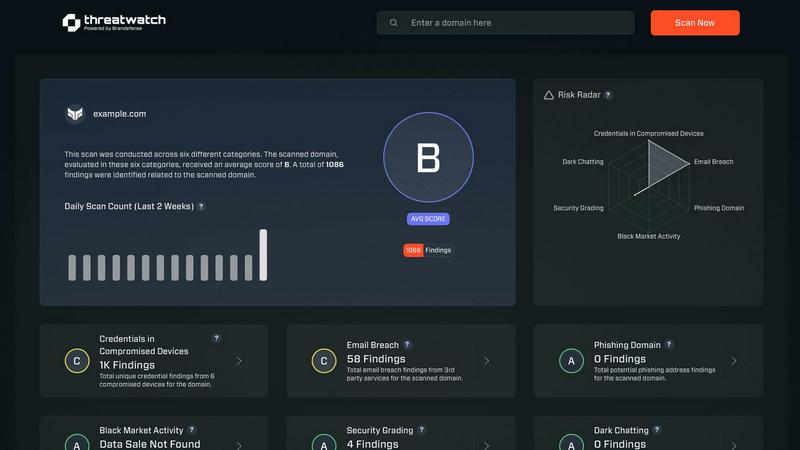
Threat Watch
Get the 411 on your cyber health and spot threats before they become a major oof.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Say goodbye to blind spots! Deeploy’s AI Discovery and Onboarding feature lets you discover, onboard, and manage every AI system from one user-friendly interface. It’s like having a helicopter view of your AI landscape—no more guessing where your models are hiding. You can connect any MLOps or GenAI platform, eliminating the migration pains that usually come with integrating new tech.
Control Frameworks
Navigating the complex maze of AI regulations can feel like running a marathon in flip-flops. But Deeploy’s Control Frameworks simplify the process with guided workflows that make compliance a breeze. You can choose from default frameworks like ISO 42001 or NIST AI RMF, or even whip up your own custom frameworks. Classifying risk? Easy-peasy, and you can establish accountability with straightforward approval processes.
Control Implementation
No more governance frameworks that gather dust! With Deeploy’s Control Implementation, you turn those frameworks into enforceable controls that engineers can actually follow. This means every AI system gets the right requirements without manual labor. You’ll give your engineers clear, actionable requirements and accelerate compliance by up to 90% with templates and auto-collected evidence. It's governance that actually works.
Real-Time Monitoring
Keep your AI systems in check with Deeploy’s Real-Time Monitoring feature. You can monitor AI performance live and catch issues before they mess with users or lead to compliance risks. Get instant alerts for model drift or performance drops, and identify errors before anyone else does. Plus, add tracing and guardrails to protect your LLM outputs. Now that’s peace of mind!
Threat Watch
Real-Time Threat Intel Flex
This isn't your grandma's weekly security report. Threat Watch is plugged into the matrix, serving up live, actionable insights on vulnerabilities and exposures as they happen. It's like having a direct feed to the cybersecurity underground, so you're never caught slippin'. You get instant alerts and a dashboard that updates faster than your social feed, keeping you in the know and ready to act.
Automated Cyber Health Scan
Say goodbye to manual, soul-crushing security checks. With one click on "Start my free scan," Threat Watch goes to work, automatically assessing your critical security categories. It's a full-system diagnostic that uncovers your cyber health fast, checking everything from compromised devices to leaked credentials, so you don't have to lift a finger. Get your results quicker than a TikTok deep dive.
Dark Web & Breach Detective
Threat Watch doesn't just look at the surface web; it dives deep into the sketchy corners of the internet. It actively hunts for your company's breached accounts, exposed credentials, and phishing addresses lurking on the dark web. This feature is your early warning system, letting you know if your data is being traded in digital back alleys before it's used against you.
Priority Risk Roadmap
Drowning in security alerts? Threat Watch cuts through the chaos. It doesn't just list problems; it analyzes and prioritizes risks based on what could actually hurt your business. It gives you a clear, actionable roadmap showing exactly what to fix first and how to mitigate it, turning overwhelming data into a simple to-do list for becoming cyber-strong.
Use Cases
Deeploy
Scaling AI Initiatives
For organizations looking to scale their AI efforts, Deeploy is a game-changer. It helps teams manage a growing number of AI systems without losing oversight. Imagine being able to deploy new models rapidly while ensuring they comply with regulations—that’s the power of Deeploy in action!
Compliance with AI Regulations
Navigating the labyrinth of AI regulations can be a nightmare, but with Deeploy, you can stay compliant without pulling your hair out. It helps organizations set up control frameworks that align with laws like the EU AI Act, giving you the confidence to operate in a regulated environment.
Enhancing Team Collaboration
Deeploy fosters collaboration between technical and non-technical teams by providing transparency and clarity around AI systems. Non-technical team members can understand AI outputs and contribute to discussions without needing a PhD in data science. It brings everyone onto the same page!
Rapid Model Deployment
Deploying AI models can take days or even weeks, but with Deeploy, you can cut that down to mere hours. This feature is perfect for teams that need to iterate quickly and maintain agility in their processes. Get those models out into the wild faster than ever before!
Threat Watch
The Startup Launchpad
You're a tech-savvy startup moving at light speed. Threat Watch is your co-pilot, providing automated, continuous security monitoring without needing a huge IT budget or team. It helps you build a secure foundation from day one, ensuring investor data and your killer app code are protected while you scale, so you can focus on disrupting the market, not putting out security fires.
The SMB Security Glow-Up
Running a small or medium biz means you wear all the hats, and "Chief Security Officer" probably wasn't one you signed up for. Threat Watch acts as your outsourced cyber expert, giving you enterprise-grade insights without the enterprise-grade complexity or cost. It's the perfect tool to proactively find and fix vulnerabilities before a hacker targets you as an easy mark.
The Corporate Compliance Check
For larger organizations, proving you're secure is just as important as being secure. Threat Watch delivers the comprehensive, real-time evidence and reporting you need to show auditors and board members that you're on top of your cyber health game. It simplifies compliance by continuously tracking assets and exposures across the entire digital estate.
The IT Team's Force Multiplier
Even if you have a dedicated IT squad, they're likely swamped. Threat Watch automates the tedious work of vulnerability discovery and initial assessment, freeing your experts to do what they do best: strategize and solve complex problems. It's like giving your team a super-powered sidekick that handles the scouting, so they can plan the winning battle strategy.
Overview
About Deeploy
Alright, folks, let’s talk about Deeploy, the ultimate game-changer in the wild world of AI management. Imagine you've got a sprawling jungle of AI models scattered all over your organization, from vendor solutions to homegrown creations. It's a chaotic mess, and without a solid control system, you're just asking for trouble—hello, compliance headaches and risk galore! Enter Deeploy, your trusty sidekick in the quest for AI governance. This platform gives you a sleek control center where you can oversee, manage, and monitor every AI system in your company. It’s designed for teams that are serious about scaling their AI initiatives without sacrificing control or running afoul of regulations like the EU AI Act. Deeploy helps you transform that potential compliance nightmare into a streamlined operation. With it, you're not just surviving the AI chaos; you're thriving in it, building trust and transparency along the way. So whether you're a data scientist or a compliance officer, Deeploy has your back.
About Threat Watch
Yo, welcome to the digital dojo! Threat Watch is your ultimate cybersecurity hype-man, designed to cut through the noise and give you the real-time lowdown on your organization's cyber health. Think of it as your personal digital bodyguard that's always on patrol, 24/7. This tool is for anyone with a digital footprint - from the solo entrepreneur grinding in their home office to the massive corporate squad managing a global empire. Its main flex? Giving you a crystal-clear, no-BS picture of your security status in a snap. It automates the boring, complex assessment stuff so you can spot risks faster than a viral meme spreads. By keeping a watchful eye on your assets, vulnerabilities, and shady exposures, it helps you identify what needs your attention right now and how to shut down those sneaky threats before they become a major headache. It's all about leveling up your defense game and getting that peace of mind, so you can focus on your grind without worrying about digital drama.
Frequently Asked Questions
Deeploy FAQ
What types of organizations can benefit from using Deeploy?
Deeploy is ideal for any organization that is using AI at scale—think businesses in finance, healthcare, tech, and beyond. If you have AI models running wild and need a way to manage them effectively, Deeploy is your go-to solution.
How does Deeploy ensure compliance with AI regulations?
Deeploy provides built-in control frameworks and guided workflows that help you navigate AI regulations effortlessly. You can choose from established frameworks or create custom ones tailored to your needs, ensuring you stay compliant with laws like the EU AI Act.
Can Deeploy integrate with existing MLOps platforms?
Absolutely! Deeploy is designed for flexibility and compatibility. You can connect it with any MLOps or GenAI platform, allowing you to manage your AI systems from one central interface without the hassle of painful migrations.
What kind of support does Deeploy offer for new users?
Deeploy offers comprehensive onboarding support and resources for new users, including explainer videos and documentation. Plus, you can book a demo to see how it all works, ensuring you hit the ground running with your AI governance strategy.
Threat Watch FAQ
How fast is the "fast" scan?
Super fast, like "microwave-burrito" fast. Our automated assessment engine is optimized to give you a comprehensive overview of your critical security categories in minutes, not days. You'll get actionable insights from your free scan almost instantly, so you can start leveling up your cyber health without the wait.
What exactly does Threat Watch monitor?
We keep our eyes on all the important (and sketchy) stuff! We scan for compromised devices on your network, credentials that have been breached and leaked online, phishing addresses targeting your domain, and any of your company's sensitive info popping up in dark web forums. It's a full 360-view of your digital exposure.
Do I need to be a cybersecurity expert to use this?
Absolutely not! Threat Watch is built for everyone. We translate complex cyber threats into simple, easy-to-understand insights and priority actions. The dashboard is intuitive, and the reports are clear—no PhD in hacking required. We hand you the info you need to make smart decisions, period.
Is there really a free version?
Yes, for real! You can start with our free scan to uncover your core cyber security health. It gives you a legit snapshot of your key risk areas. If you want the full, continuous protection suite with real-time alerts and deeper monitoring, we have upgraded plans to match your needs and budget.
Alternatives
Deeploy Alternatives
Deeploy is your go-to admin panel for managing all the AI chaos in your organization. As a centralized control center, it helps you oversee and govern your scattered AI models, whether they come from vendors or in-house data scientists. Users often seek alternatives to Deeploy due to reasons like budget constraints, specific feature requirements, or unique platform needs that don’t align with what Deeploy offers. When hunting for an alternative, consider factors like ease of use, scalability, and how well it integrates with your existing tools. You want something that keeps your AI game strong without the compliance headaches.
Threat Watch Alternatives
So, you've heard about Threat Watch, the cybersecurity sidekick that's all about giving you that real-time intel on your digital health. It's a Business Intelligence tool that basically acts like your personal cyber bouncer, spotting vulnerabilities and dark web drama before it crashes your party. It's a solid pick for getting your security game on point. But hey, one size doesn't fit all in the tech world, right? People start hunting for alternatives for all sorts of reasons. Maybe the price tag is doing a number on your budget, or you need a feature that's just not in the current lineup. Sometimes it's about platform compatibility—you need something that vibes perfectly with your existing tech stack. When you're scrolling through the options, keep your eyes peeled for a few key things. You'll wanna check if the tool gives you that real-time, actionable intel, how slick the automation is (because nobody has time for manual checks), and whether it covers your specific worries, like phishing scams or dark web surveillance. It's all about finding that perfect match for your team's vibe and needs.
