iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
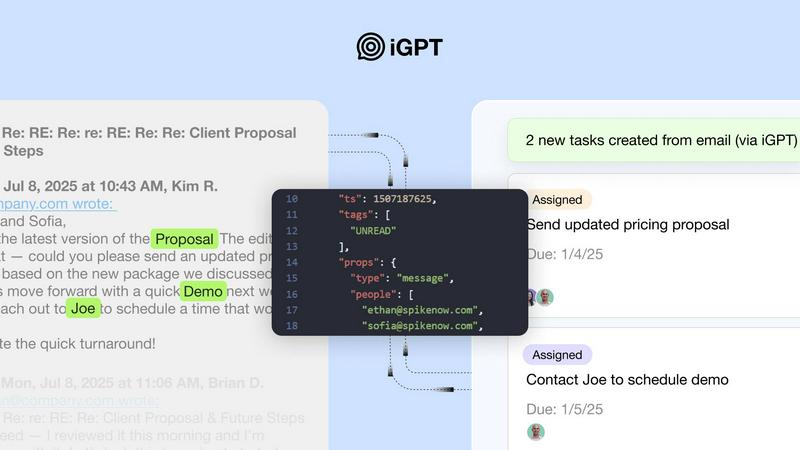
iGPT gives your AI agents the real context from emails so they actually work.
Last updated: March 1, 2026
Threat Watch
Get the 411 on your cyber health and spot threats before they become a major oof.
Last updated: March 1, 2026
Visual Comparison
iGPT
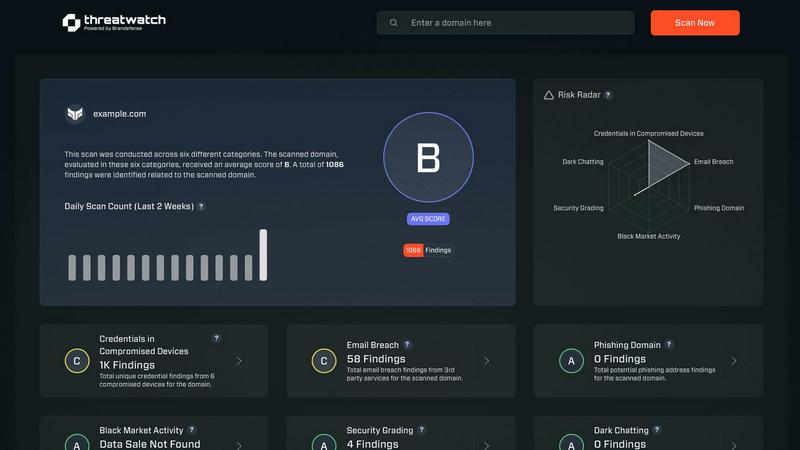
Threat Watch
Feature Comparison
iGPT
One Unified Endpoint to Rule Them All
Forget stitching together a RAG pipeline from a dozen different services. iGPT replaces multi-endpoint retrieval chaos with one natural language request. You just ask a question like "What are the open action items?" and the API handles the entire pipeline: retrieval, context shaping, and reasoning, all in one call. No prompt chains, no tuning, just answers. It's the developer experience dream.
Thread Reconstruction & Attachment Processing
Email threads are a tangled mess across time, people, and files. iGPT automatically rebuilds those conversations, understanding who said what and when. Plus, it doesn't just ignore attachments; it processes them deeply, extracting text, data, and structure from PDFs, docs, and spreadsheets, so your AI gets the full picture, not just the email body.
Hybrid Retrieval That Actually Works
iGPT doesn't bet on just one search method. It uses a hybrid approach combining semantic understanding, keyword matching, and filters, all scored and reranked in a single call. This means it finds the relevant needle in the haystack, whether you're searching by concept, a specific phrase, or a person's name.
Context Shaping & Zero Data Retention
iGPT optimizes the context window for your LLM automatically, so you don't have to be a prompt engineering wizard. Even better, it's built with trust: it operates with zero data retention. Each inference is processed in memory, and your inputs, prompts, and outputs are never stored on their servers. Your secrets stay yours.
Threat Watch
Real-Time Threat Intel Flex
This isn't your grandma's weekly security report. Threat Watch is plugged into the matrix, serving up live, actionable insights on vulnerabilities and exposures as they happen. It's like having a direct feed to the cybersecurity underground, so you're never caught slippin'. You get instant alerts and a dashboard that updates faster than your social feed, keeping you in the know and ready to act.
Automated Cyber Health Scan
Say goodbye to manual, soul-crushing security checks. With one click on "Start my free scan," Threat Watch goes to work, automatically assessing your critical security categories. It's a full-system diagnostic that uncovers your cyber health fast, checking everything from compromised devices to leaked credentials, so you don't have to lift a finger. Get your results quicker than a TikTok deep dive.
Dark Web & Breach Detective
Threat Watch doesn't just look at the surface web; it dives deep into the sketchy corners of the internet. It actively hunts for your company's breached accounts, exposed credentials, and phishing addresses lurking on the dark web. This feature is your early warning system, letting you know if your data is being traded in digital back alleys before it's used against you.
Priority Risk Roadmap
Drowning in security alerts? Threat Watch cuts through the chaos. It doesn't just list problems; it analyzes and prioritizes risks based on what could actually hurt your business. It gives you a clear, actionable roadmap showing exactly what to fix first and how to mitigate it, turning overwhelming data into a simple to-do list for becoming cyber-strong.
Use Cases
iGPT
The Ultimate Support Copilot
Rebuild a customer's entire story instantly, no matter how long the email chain. iGPT can pull context across months of back-and-forth, including attached support tickets and invoices, to give support agents or an AI copilot the full history and tone shifts, slashing resolution time.
Autonomous Sales & CRM Agents
Build deal-room bots that actually understand deal momentum. iGPT can extract key decisions, identify owners, track commitments, and analyze sentiment directly from email threads and attached contracts, giving your sales AI the context to prioritize and act without human babysitting.
Workflow Automation From Chaos
Turn messy email threads into structured tasks, deadlines, and approvals automatically. Flag what's stuck, identify missing sign-offs from attached PDFs, and create project tickets. It turns your inbox into an automated workflow engine without the manual slog.
Compliance & Audit Trail Clarity
Need to trace who approved what and when? iGPT creates an instant, citable audit trail. Find feedback, rationale, and official approvals by searching natural language across emails and attachments, making compliance reviews a breeze instead of a nightmare.
Threat Watch
The Startup Launchpad
You're a tech-savvy startup moving at light speed. Threat Watch is your co-pilot, providing automated, continuous security monitoring without needing a huge IT budget or team. It helps you build a secure foundation from day one, ensuring investor data and your killer app code are protected while you scale, so you can focus on disrupting the market, not putting out security fires.
The SMB Security Glow-Up
Running a small or medium biz means you wear all the hats, and "Chief Security Officer" probably wasn't one you signed up for. Threat Watch acts as your outsourced cyber expert, giving you enterprise-grade insights without the enterprise-grade complexity or cost. It's the perfect tool to proactively find and fix vulnerabilities before a hacker targets you as an easy mark.
The Corporate Compliance Check
For larger organizations, proving you're secure is just as important as being secure. Threat Watch delivers the comprehensive, real-time evidence and reporting you need to show auditors and board members that you're on top of your cyber health game. It simplifies compliance by continuously tracking assets and exposures across the entire digital estate.
The IT Team's Force Multiplier
Even if you have a dedicated IT squad, they're likely swamped. Threat Watch automates the tedious work of vulnerability discovery and initial assessment, freeing your experts to do what they do best: strategize and solve complex problems. It's like giving your team a super-powered sidekick that handles the scouting, so they can plan the winning battle strategy.
Overview
About iGPT
Let's be real: email is the chaotic, messy, beautiful beast where actual work gets done. It's also the place where most AI tools absolutely faceplant. Trying to get an AI agent to understand a sprawling email thread with attachments is like asking a goldfish to do your taxes. iGPT fixes that. It's the email intelligence API that finally gives your AI agents and workflows the context they desperately need. Think of it as the ultimate translator between your messy human communication and your clean, logical AI systems. Built for developers and enterprises building the next wave of agentic AI, iGPT is the cheat code for building AI that actually understands how work happens. The main flex? You skip all the painful stuff: no parsing, no chunking, no building your own vector stores. You just send a single, simple API call asking a question in plain English, and iGPT does the heavy lifting. It fetches, deeply understands, and shapes the context from your emails and attached docs, delivering a crisp, cited answer ready for your LLM to reason with. It's built for the builders of sales bots, deal analyzers, customer success automators, you name it. If you're tired of AI agents being clueless about your inbox, iGPT is your plug.
About Threat Watch
Yo, welcome to the digital dojo! Threat Watch is your ultimate cybersecurity hype-man, designed to cut through the noise and give you the real-time lowdown on your organization's cyber health. Think of it as your personal digital bodyguard that's always on patrol, 24/7. This tool is for anyone with a digital footprint - from the solo entrepreneur grinding in their home office to the massive corporate squad managing a global empire. Its main flex? Giving you a crystal-clear, no-BS picture of your security status in a snap. It automates the boring, complex assessment stuff so you can spot risks faster than a viral meme spreads. By keeping a watchful eye on your assets, vulnerabilities, and shady exposures, it helps you identify what needs your attention right now and how to shut down those sneaky threats before they become a major headache. It's all about leveling up your defense game and getting that peace of mind, so you can focus on your grind without worrying about digital drama.
Frequently Asked Questions
iGPT FAQ
How do I get started with the iGPT API?
It's designed to be stupid simple. Grab your API key, check out the SDK and the live playground to test requests and responses. You can connect email sources and start asking questions in minutes. They even offer $10 in free credits to play with, no credit card required.
Is my company's email data safe with iGPT?
Absolutely. iGPT is built with enterprise-grade security. They have a strict zero-data training policy (your data never trains their models), OAuth-only processing with Role-Based Access Control (RBAC), and most importantly, zero data retention. Your data is processed in memory and never stored.
What kinds of file attachments can iGPT process?
iGPT is a beast at processing attachments. It can extract text and data from a wide range of documents including PDFs, spreadsheets (like Excel and Sheets), presentations, and Word docs. It understands the structure so your AI gets the context from inside the files, not just the filenames.
Can iGPT handle real-time, incoming emails?
Yes! iGPT features real-time ingestion, meaning it indexes new messages and attachments instantly as they hit your connected mailbox. This ensures the context it provides is always up-to-date, so your AI agents are working with the latest info, not yesterday's news.
Threat Watch FAQ
How fast is the "fast" scan?
Super fast, like "microwave-burrito" fast. Our automated assessment engine is optimized to give you a comprehensive overview of your critical security categories in minutes, not days. You'll get actionable insights from your free scan almost instantly, so you can start leveling up your cyber health without the wait.
What exactly does Threat Watch monitor?
We keep our eyes on all the important (and sketchy) stuff! We scan for compromised devices on your network, credentials that have been breached and leaked online, phishing addresses targeting your domain, and any of your company's sensitive info popping up in dark web forums. It's a full 360-view of your digital exposure.
Do I need to be a cybersecurity expert to use this?
Absolutely not! Threat Watch is built for everyone. We translate complex cyber threats into simple, easy-to-understand insights and priority actions. The dashboard is intuitive, and the reports are clear—no PhD in hacking required. We hand you the info you need to make smart decisions, period.
Is there really a free version?
Yes, for real! You can start with our free scan to uncover your core cyber security health. It gives you a legit snapshot of your key risk areas. If you want the full, continuous protection suite with real-time alerts and deeper monitoring, we have upgraded plans to match your needs and budget.
Alternatives
iGPT Alternatives
So you've heard about iGPT, the email intelligence API that's basically a cheat code for AI agents. It lives in the Business Intelligence world, but its real job is translating the chaotic mess of your inbox into clean, usable context for your AI workflows. It's the tool that stops your bots from faceplanting in long email threads. People hunt for alternatives for all the usual reasons. Maybe the pricing doesn't fit their startup budget, or they need a feature that's still on the roadmap. Sometimes a team is locked into a specific platform like Google Workspace and needs a native solution, or they want more hands-on control over the data pipeline instead of a magic one-call endpoint. When you're shopping around, don't just look at the sticker price. You gotta ask the real questions. Can it actually read your email threads and attachments, or does it just skim subject lines? How much manual setup and "prompt engineering" will your devs need to do? Most importantly, does it solve the core problem of giving your AI the real, messy context from where work actually happens, or is it just another layer of complexity?
Threat Watch Alternatives
So, you've heard about Threat Watch, the cybersecurity sidekick that's all about giving you that real-time intel on your digital health. It's a Business Intelligence tool that basically acts like your personal cyber bouncer, spotting vulnerabilities and dark web drama before it crashes your party. It's a solid pick for getting your security game on point. But hey, one size doesn't fit all in the tech world, right? People start hunting for alternatives for all sorts of reasons. Maybe the price tag is doing a number on your budget, or you need a feature that's just not in the current lineup. Sometimes it's about platform compatibility—you need something that vibes perfectly with your existing tech stack. When you're scrolling through the options, keep your eyes peeled for a few key things. You'll wanna check if the tool gives you that real-time, actionable intel, how slick the automation is (because nobody has time for manual checks), and whether it covers your specific worries, like phishing scams or dark web surveillance. It's all about finding that perfect match for your team's vibe and needs.
